You might not love hard math problems. Let’s be honest, most of us don’t. Maybe you enjoy the suffering of a complex equation, but if you’re like the rest of us, you probably avoid it. But whether you like it or not, you benefit massively from the fact that incredibly hard math problems exist.
In fact, we all do. These seemingly torturous math puzzles are the very foundation of modern cryptography, which is the ultimate way we keep our secrets actually secret. Think about the stuff you want to stay private: your personally identifiable information, your personal health records, your bank details, intellectual property, and sensitive business records. Without the ability to lock this data down, the internet as we know it would simply cease to exist. There would be no way to prove you are really you when you log into your bank, and absolutely no way to keep your personal information from becoming public.
So, what do I mean by “hard math problems” in this context? Let’s start with a few examples to set the stage.
The Math That Protects You Today (And Why It’s in Danger)
If I ask you to add 34 and 51, you can probably do that in your head in a split second. That is an easy math problem. If we based our internet security on something that simple, we wouldn’t have much of a secret, because any hacker with a basic calculator could crack it open.
Let’s try something a little harder. Let’s say I ask you to pick two prime numbers (numbers only divisible by 1 and themselves) that multiply together to equal 21. You can probably guess that 7 and 3 give you 21. Not exactly a mind-bending challenge, right?
But what if I asked you to find the two prime factors of a 600-digit number?
Now your mind is blown. You can’t just guess it. In fact, the best supercomputers we have on the planet today would take thousands of years—possibly longer than the lifespan of the universe—to solve that specific problem.
Because it’s so hard for classical computers, we built our modern digital world on top of it. Algorithms like RSA use this exact type of math to secure your web browsing, your emails, and your financial transactions.
But there’s a new monster hiding in the shadows: the quantum computer. A sufficiently powerful quantum computer doesn’t care about that 600-digit number. It could solve that same problem in a matter of hours. If a quantum system can break that math easily, it means our current cryptography breaks easily. And just like that, all the secrecy we rely on evaporates.
So, what is the solution? How do we fight a machine that breaks the unbreakable?
The answer is a concept called lattice cryptography. It is based on hard math problems that are so massively more difficult than finding prime factors that even a quantum computer throws a tantrum trying to solve them. Let’s break down how this works, without needing a math degree to understand it.
Table of Contents
The Chess Analogy: Understanding Lattice Basics
To understand how lattice crypto works, let’s step away from the computer screen for a second and play a game of chess. Well, not a full game—just a thought experiment using the pieces.
Imagine you have a single knight on a chessboard. You know how a knight moves: it goes over one square and up two, or over two squares and up one. If I tell you to move that knight to a specific, valid square on the board, that’s an easy math problem. You just calculate the moves.
But what if I change the rules? What if I point to a spot on the board that isn’t exactly in the center of any square? It’s floating somewhere in the empty space between four squares. I tell you, “Get as close to this exact spot as possible using only knight moves.”
Now you have a problem. You could go over two and up one, and you miss the spot by a little bit. You could try going over two and up one, then up one and over two, and you miss it in a different direction. You could try routing your knight all the way around the board and coming back from another angle to get a fraction of a millimeter closer.
Do you see what we just did there? We took a simple rule (a knight’s move) and introduced complexity by asking for an approximation of a target that doesn’t fit the grid.
Now, let’s make it harder. Instead of fixed moves like “over two, up one,” let’s turn those into variables: x moves one way, y moves another. You don’t know what x and y are, you just have to guess the combination that lands closest to that floating spot.
Still think you can solve it? Let’s take this 2D chessboard and turn it into a thousand-dimensional space.
Now your mind is truly blown. You can’t even visualize a thousand dimensions, let alone calculate knight moves in it. Then, we add noise—that floating spot that isn’t on the grid. That noise, combined with massive dimensions and unknown variables, takes a simple puzzle and turns it into a nightmare.
In the world of cryptography, this specific nightmare is called Learning with Errors (LWE). And it is the absolute backbone of lattice crypto.
How Lattices Actually Work (Without the Migraine)
Let’s take our chessboard complexity and apply it to actual lattices. Don’t worry, I promised to keep the deep math to a minimum, so we’re just going to look at the high-level concepts.
What exactly is a lattice? Think of it as an infinite grid in multidimensional space. It starts with an origin point (like the corner of a piece of graph paper). From that origin point, you draw a couple of arrows called basis vectors.
Imagine one arrow pointing diagonally up at a 45-degree angle (let’s make it green), and another arrow pointing straight horizontally (let’s make it blue, and twice as long as the green one).
Any combination of these two arrows creates a new dot in space.
- One green arrow gets you to Dot A.
- One blue arrow gets you to Dot B.
- Two green arrows get you to Dot C.
- One green plus one blue gets you to Dot D.
If you keep adding and subtracting these green and blue arrows in every possible combination, you eventually fill the space with an infinite grid of perfectly aligned dots. That grid is your lattice.
Now, here is the hard problem that keeps your data safe.
I am going to give you a secret point that is not perfectly aligned with your grid. It’s floating in space, just like the weird spot on our chessboard. My question to you is: Which combination of green and blue arrows gets you closest to that secret point?
In a simple 2D space with just two arrows, you can probably eyeball it. But remember, we need this to secure the entire internet. So, we aren’t playing with two arrows in two dimensions. We are playing with hundreds of arrows in a thousand dimensions.
When you add the “noise” (the secret point not being on the grid), there are seemingly infinite combinations of arrows that get you “close” to the target, but only one exact combination that gets you the closest. Finding that exact combination requires brute-forcing through an astronomical number of possibilities.
To help visualize how this scales from “easy” to “impossible,” look at the diagram below.
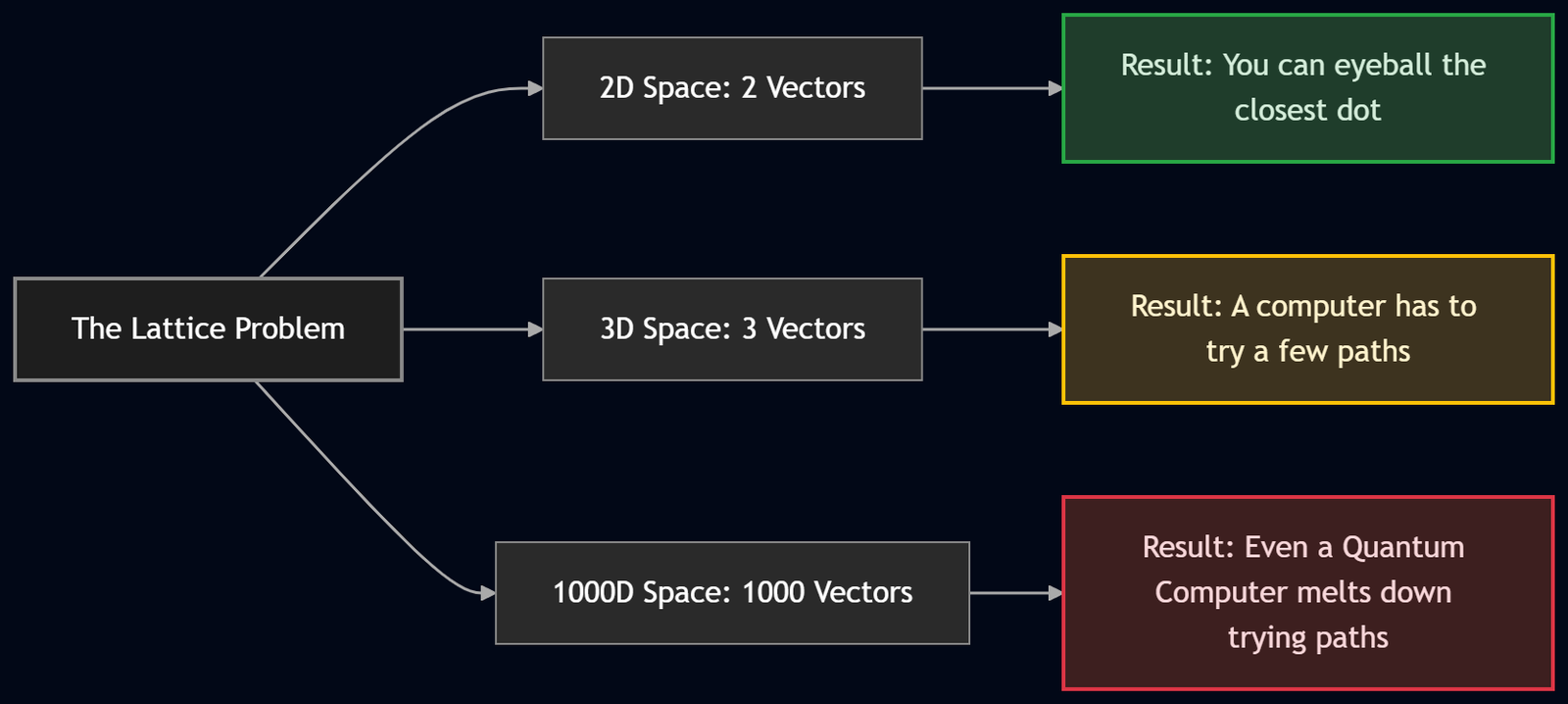
A good cryptographic algorithm guarantees there are no shortcuts. You can’t reverse-engineer the answer. You just have to guess, check, guess, check, over and over until the heat death of the universe. A supercomputer can’t solve it. And here is the magic of lattice cryptography: a quantum computer can’t solve it either.
If you make the lattice complex enough and introduce enough noise, a quantum system that can effortlessly break our current encryption will still be utterly defeated by a lattice. That is the foundation of quantum-safe crypto.
Why Quantum Computers Hate Lattices
To understand why lattices survive the quantum apocalypse while RSA crumbles, you have to understand what quantum computers are actually good at.
Quantum computers aren’t just “faster” versions of regular computers. They are good at very specific types of math—specifically, they are brilliant at finding patterns in periodic, repeating structures. Factoring a large number into primes is essentially a pattern-matching problem, which is why a quantum computer eats it for breakfast.
But look at our lattice problem again. We took a structured grid and we threw a random handful of dirt into the gears by adding noise (the secret point that isn’t on the grid).
Noise destroys the repeating patterns. When a quantum computer looks at a high-dimensional lattice with errors, it doesn’t see a pattern it can exploit; it just sees chaotic, random noise. It still has to rely on brute force, trying one combination after another. And because there are too many combinations, it fails.
Sometimes, difficult actually means good. The harder the math problem, the stronger the crypto—because it forces an attacker into a brute-force guessing game. And that is a massive win for the good guys.
The Good News: You Don’t Need a Quantum Computer to Defend
Here is probably the best news you’ll hear all day: You do not need to buy a quantum computer to protect yourself from a quantum computer.
The smart cryptographers of the world have already done the heavy lifting for us. About ten years ago, the U.S. National Institute of Standards and Technology (NIST) realized the quantum threat was looming. They put out a call to the world’s best mathematicians and cryptographers, asking for new algorithms that quantum computers wouldn’t be able to break.
After a decade of rigorous testing, hacking, and peer-reviewing, the best minds in the world coalesced around a set of quantum-safe crypto algorithms. Most of these winning algorithms are based on the lattice arithmetic we just talked about.
These algorithms are out in the wild right now. They are in open-source repositories. They are becoming industry standards. And most importantly, they run perfectly fine on the normal, classical servers and laptops we use today. You can start deploying them right now.
Your Action Plan: Surviving “Q Day”
“Q Day” is the theoretical day in the future when a sufficiently powerful quantum computer comes online and breaks our existing crypto. It sounds like a sci-fi movie, but governments and cybersecurity professionals are treating it as an absolute certainty. It’s not a matter of if, but when.
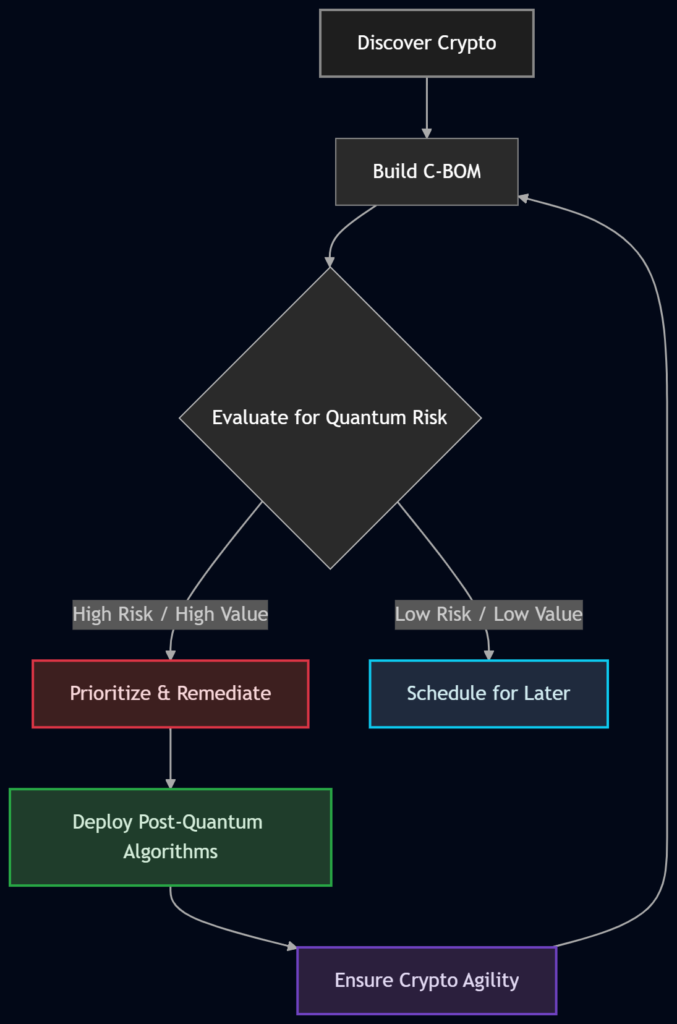
So, what should you be doing right now to implement post-quantum cryptography (PQC)? It starts with a structured, step-by-step approach.
Step 1: Discovery
You cannot fix what you do not know exists. You need to map out every single instance of cryptography in your environment. Where is data being encrypted? Where are digital signatures being used to verify identity? Where are secure communication channels established?
Step 2: Build Your Crypto Bill of Materials (C-BOM)
Out of that discovery phase, you create a C-BOM. Think of this like an ingredient list for your organization’s security. It is a detailed inventory of every cryptographic algorithm, key length, and protocol you are currently using.
Step 3: Evaluate and Prioritize
Look at your C-BOM and ask: “If a quantum computer existed today, which of these would break?” You must prioritize fixing the most sensitive data first. You aren’t going to fix everything in one day—most large organizations have hundreds or thousands of instances of custom crypto. Go after the crown jewels first.
Step 4: Remediation
This is the actual fix. Do you need to update your software to support new key lengths? Do you need to swap out the old RSA algorithm entirely for a new lattice-based algorithm? This is where the heavy lifting happens.
Step 5: Repeat (Achieving Crypto Agility)
This is the ultimate goal. You don’t want to go through this painful process ever again. Crypto agility means building your systems so that if an algorithm is suddenly found to have a weakness tomorrow, you can swap it out for a new one quickly without tearing apart your entire infrastructure.
Here is a simplified look at that lifecycle:
| Phase | Action | Goal | Example |
|---|---|---|---|
| Discovery | Scan networks and apps | Find all hidden crypto uses | Finding an old TLS 1.2 endpoint on a legacy server |
| C-BOM Creation | Catalog the findings | Create a central inventory | Logging: “Server A uses RSA-2048 for signatures” |
| Evaluation | Assess quantum vulnerability | Find the weakest links | Realizing RSA-2048 is highly vulnerable to Q-Day |
| Prioritization | Rank by data sensitivity | Protect the most critical data first | Prioritizing patient health records over public marketing data |
| Remediation | Swap algorithms | Implement Post-Quantum Crypto | Upgrading Server A to a NIST-approved lattice algorithm |
| Agility | Automate and modularize | Make future swaps painless | Designing APIs so crypto libraries can be hot-swapped |
The Real Nightmare: “Harvest Now, Decrypt Later”
If you are thinking, “Well, quantum computers aren’t quite ready yet, so I’ll just fix my security next year,” you are falling into the most dangerous trap in cybersecurity.
There is a four-letter phrase that should keep every IT director and chief information security officer awake at night: Harvest Now, Decrypt Later (HNDL).
Here is how it works. Hackers—often state-sponsored ones—don’t need a quantum computer today to steal your data. They know that eventually, quantum computers will exist. So, right now, today, they are breaking into networks, finding your encrypted databases, and simply copying the encrypted files. They can’t read them yet, but they hoard them on massive hard drives.
Then, they wait.
Five years from now, when a quantum computer comes online, they take those hoarded files and run them through the quantum machine. The encryption breaks, and suddenly they have access to five years’ worth of your stolen intellectual property, military secrets, or financial data.
If your data is sensitive enough to be encrypted today, it is sensitive enough to be stolen today. We need to start securing our data with lattice cryptography right now, unless, of course, you happen to have a time machine. If you do have a time machine, you could just go back to the past and re-encrypt all your data before it was stolen. But if you take that option, make sure you come back to the present, because we’d miss you.
Wrapping Up
At the end of the day, the transition to post-quantum security isn’t a technology problem; it’s a math problem that has already been solved. We have the algorithms. We have the standards. We understand that the massive complexity of multi-dimensional lattices, mixed with a little bit of chaotic noise, creates a wall that even the most advanced quantum computers cannot climb.
The challenge now is simply logistics. It’s about doing the discovery, building your Crypto Bill of Materials, prioritizing your most sensitive assets, and moving toward crypto agility. Difficult math is what keeps the bad guys out, but it’s going to take good, old-fashioned hard work from IT professionals to deploy that math before Q Day arrives.
Start now. Because the harvest is already happening.
References:
- Lattice-Based Cryptography: https://en.wikipedia.org/wiki/Lattice-based_cryptography
- Quantum Safe Algorithms: https://cloudcusp.com/blogs/quantum-safe-algorithm-3-proven-ways-to-save-data/
FAQs
What exactly is post-quantum cryptography?
Post-quantum cryptography is just a fancy way of saying “new locks for future skeleton keys.” It is a set of new math problems designed to protect our data from quantum computers. Even though we are using it on regular computers right now, it is called “post-quantum” because it is specifically built to survive the future threats that quantum machines will bring.
Why should I care about quantum computers right now? They aren’t even fully built yet.
You should care because hackers are playing the long game with a strategy called “harvest now, decrypt later.” They are breaking into networks today, finding your encrypted files, and simply copying them. They cannot read the files yet, but they are hoarding them on hard drives. The moment a quantum computer is built, they will use it to unlock all that stolen data. If your data is sensitive today, it needs protection today.
What is lattice cryptography, and why is it so special?
Imagine an infinite grid, but instead of being flat on a piece of paper, it exists in a space with a thousand dimensions. Now, imagine trying to find the closest grid point to a random floating speck of dust. There are trillions of paths you could take, and absolutely no shortcut to find the right one. That guessing game in a thousand dimensions is lattice cryptography, and it is a nightmare for computers to solve.
Do I need to buy a quantum computer to defend against a quantum computer?
Not at all! That is one of the best parts about this entire situation. The math behind lattice cryptography runs perfectly fine on the normal, classical servers and laptops we already own. You do not need to go out and buy millions of dollars worth of futuristic quantum hardware to keep your secrets safe.
How do quantum computers actually break our current internet security?
The security we use today relies on a specific math puzzle: taking a massive number and figuring out which two prime numbers multiply together to create it. Regular computers stink at this and take thousands of years to guess. Quantum computers, however, are uniquely designed to spot hidden patterns, allowing them to solve that puzzle in hours instead of millennia.
Why can’t quantum computers just break lattice cryptography too?
Because lattice cryptography intentionally introduces “noise” (random errors) into the math. Quantum computers are brilliant at finding neat, repeating patterns. But the noise completely ruins the pattern. It forces the quantum computer into a brute-force guessing game, and even a quantum computer does not have enough time in the universe to guess its way through a thousand dimensions of noise.
What is a Crypto Bill of Materials, or C-BOM?
Think of it like a nutritional label, but for your company’s software security. A C-BOM is a detailed, organized list of everywhere your organization uses encryption, passwords, or digital signatures. You cannot fix your weak security spots if you do not even know they exist, so making this list is always step one.
What does “crypto agility” mean?
Crypto agility means building your tech systems so they have plug-and-play security. If a new math algorithm is invented, or an old one is suddenly broken, you can easily swap out the old “lock” for a new one without having to tear down your entire digital infrastructure to do it. It is the ultimate goal of upgrading your security.
What is “Q Day”?
“Q Day” is the unofficial term for the day a quantum computer finally becomes powerful enough to crack the standard encryption that currently runs the internet. Cybersecurity experts do not know the exact date it will happen, but they treat it as an absolute certainty that it will happen eventually.
Is this just a problem for big tech companies and the government?
Absolutely not. If you run a small business, handle patient health records, or just use online banking, you are relying on the exact same broken math as the big corporations. Hackers know that small businesses are easy targets, which makes them prime candidates for data harvesting. Everyone needs to pay attention to this shift.