We’ve all been there. You’re scrolling through social media or watching a video, and suddenly, an ad pops up. “Your privacy is at risk!” it screams. “Buy this VPN now to become invisible online!” It sounds tempting, doesn’t it? The idea that you can download a piece of software and suddenly vanish from the digital world is a powerful selling point. But if you’ve ever wondered what is actually happening behind the scenes, you’re in the right place.
Recently, I found myself deep in a discussion about this very topic. It started with a simple question: Does a VPN really protect privacy? The answers I found—and the misconceptions I had to correct—revealed a landscape that is far more nuanced than most marketing slogans would have you believe. Today, we are going to strip away the buzzwords and dig into the reality of Personal VPNs, how they interact with encryption, and what they actually mean for your data security.
This isn’t just a technical overview; it’s a conversation about trust, architecture, and the myths that lead us into a false sense of security.
Table of Contents
The Foundation: How the Internet Actually Works
Before we can understand what a Virtual Private Network (VPN) does, we have to look at how your internet connection works without one. It sounds basic, but this is where most of the confusion starts.
Imagine you are sitting at home, sipping coffee, and you decide to visit your favorite website. You type the address into your browser and hit Enter. Here is the journey your request takes:
- The Request: Your computer creates a packet of data. Think of this like a physical envelope containing a letter.
- The ISP: Your computer sends this envelope to your Internet Service Provider (ISP). The ISP is like your local post office. They look at the address on the envelope and send it out into the world.
- The Destination: The envelope travels across the internet and arrives at the website’s server. The server opens it, reads the request, and sends a package back to you.
Most of us know that websites use HTTPS (Hypertext Transfer Protocol Secure). You’ve seen the little lock icon in your browser bar. This is a good thing. It means that the “letter” inside the envelope is encrypted. If a hacker intercepted the envelope while it was traveling between the ISP and the website, they couldn’t read the letter inside.
But here is the catch: The envelope itself is still readable.
Headers vs. Payloads
To understand this better, let’s look at how data packets are structured. In networking, a packet is divided into two main parts: the Header and the Payload.
- The Payload: This is the actual data—the letter inside the envelope. If you are entering a password or credit card number, HTTPS encrypts this part. Nobody can see your password.
- The Header: This is the address label on the envelope. It contains the Source IP address (that’s you) and the Destination IP address (the website you are visiting).
Even with HTTPS, the Header must remain readable. If the envelope didn’t have a clear address on it, the post office (the ISP) wouldn’t know where to send it.
The ISP’s View
So, what does your ISP see? They see the Header. They know who you are (your IP address) and exactly which websites you are connecting to. They might not know what you are typing (the encrypted Payload), but they know your habits.
Why does this matter?
- Data Sales: ISPs are corporations. Many collect metadata about your browsing habits to build a profile for advertising.
- Data Breaches: If your ISP is hacked, your browsing history could become public.
- Legal Requests: In many jurisdictions, ISPs are legally required to hand over logs of your activity if served with a court order.
This is where the VPN comes into play.
The VPN Solution: The “Tunnel” Effect
Now, let’s introduce the Virtual Private Network. A lot of people think a VPN is a magic invisibility cloak. It’s not. It is essentially a redirect service.
When you subscribe to a VPN service, you install a piece of software on your device called a client. This client creates a secure, encrypted “tunnel” between your device and a server run by the VPN provider.
Let’s visualize this process compared to the standard connection.
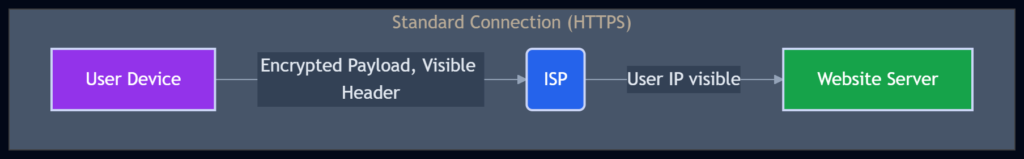
In the standard connection above, your data goes straight through the ISP. They see the destination IP clearly.
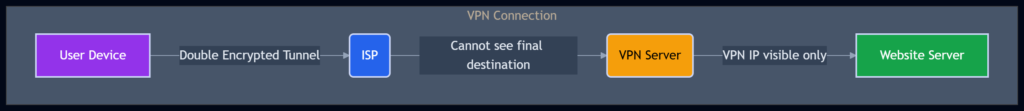
Now, look at what happens with a VPN:
How the Magic Happens
When you turn on your VPN client, the following steps occur:
- Encryption: Before any packet leaves your computer, the VPN client wraps the entire packet (Header and Payload) inside a new packet. This is like putting your addressed envelope inside a second, unbreakable steel box.
- The Redirect: The outer box is addressed to the VPN server.
- The ISP’s Blindness: Your ISP receives this steel box. They can see you are sending data to the VPN server, but they cannot see the inner envelope. They don’t know which website you are actually visiting.
- The Decryption: The VPN server receives the box, unlocks it, opens the inner envelope, and forwards your request to the website.
To the website, the request appears to be coming from the VPN server, not your home computer. This effectively masks your geographic location and personal IP address.
A Correction: The “Double Tunnel” Myth
In the past, I—and many others—explained this process by suggesting that the VPN provider creates a second encrypted tunnel between their server and the final website. This would be a “double hop” of encryption.
However, this is generally not how standard personal VPNs work. In reality, the VPN provider usually acts as a standard proxy.
- Leg 1 (You to VPN): Heavily encrypted. Your ISP is blinded.
- Leg 2 (VPN to Website): Standard HTTPS connection (if the site supports it).
This distinction is crucial. It means that once your traffic leaves the VPN server heading to the destination website, it is subject to the same rules as any other traffic. The VPN provider is now the one making the request on your behalf.
The Code Behind the Curtain (Simplified)
For those of you who like to see how things work “under the hood,” let’s look at a simplified pseudo-code representation of how a VPN client processes a packet compared to a standard browser request.
Standard Request (No VPN):
def send_packet_standard(destination_ip, data):
# Create a packet with visible headers
header = {
"Source_IP": "192.168.1.1", # This is YOU
"Dest_IP": destination_ip # This is the WEBSITE
}
# Encrypt only the data (HTTPS)
payload = encrypt_https(data)
# Send to ISP
isp.send(header, payload)
# Result: ISP knows you visited destination_ipVPN Request:
def send_packet_vpn(vpn_server_ip, destination_ip, data):
# 1. Create the 'inner' packet (what you actually want to do)
inner_header = {
"Source_IP": "192.168.1.1",
"Dest_IP": destination_ip
}
inner_payload = encrypt_https(data)
# 2. Wrap the WHOLE thing (header + payload) in VPN encryption
# This creates a 'tunnel'
tunnel_data = encrypt_vpn_protocol(inner_header, inner_payload)
# 3. Create the 'outer' header for the ISP to read
outer_header = {
"Source_IP": "192.168.1.1",
"Dest_IP": vpn_server_ip # The ISP only sees this!
}
# 4. Send to ISP
isp.send(outer_header, tunnel_data)
# Result: ISP only sees you talking to vpn_server_ipThis code illustrates the concept of encapsulation. By wrapping the original header inside the payload of the outer packet, you hide your browsing destination from the ISP.
The “Transfer of Trust”: The Biggest Myth of All
Here is the part where we have a real talk. We discussed why you might not trust your ISP. Maybe they sell your data, or you just don’t like them knowing your business.
But when you use a VPN, you aren’t eliminating the risk of data logging; you are simply transferring the risk.
Let’s compare the two entities:
| Feature | Your ISP | Your VPN Provider |
|---|---|---|
| Visibility | Sees every site you visit. | Sees every site you visit. |
| Identity | Knows your name, address, and billing info. | Knows your name, address, and billing info. |
| Incentive | Often monetizes data; legally compelled to log. | Claims “No Logs”; varied business models. |
| Jurisdiction | Subject to local laws. | Subject to their country’s laws (varies). |
You are effectively moving your internet traffic from a “public” road (ISP) to a “private” road (VPN). The private road hides you from the people on the public road, but the owner of the private road can still see everything you are doing.
The “Free VPN” Trap
If you aren’t paying for the product, you are the product.
This is the golden rule of the internet. Running a VPN network costs a fortune in bandwidth and server maintenance. If a VPN provider gives you their service for free, how are they paying the bills?
- Selling Metadata: They might be logging your activity and selling that data to advertisers—the exact thing you were trying to avoid!
- Ad Injection: Some free VPNs inject ads into your browsing sessions.
When you pay for a VPN, you are paying for the service of privacy. When you use a free VPN, you are often trading privacy for “free” access.
Anonymity vs. Privacy: Know the Difference
This is another area where myths run wild. People often think a VPN makes them anonymous. It does not.
Privacy means people can’t see what you are doing.
Anonymity means people can’t see who is doing it.
A VPN gives you privacy from your ISP and the website (to an extent), but it does not grant total anonymity.
- Cookies: If you log into your Google account while using a VPN, Google knows exactly who you are. The VPN didn’t hide your identity; it only hid the route you took to get there.
- Browser Fingerprinting: Websites can identify you based on your browser version, screen resolution, and installed fonts, even without your IP address.
- The VPN Provider: As mentioned, they know who you are.
VPNs vs. Tor: The Heavyweight Matchup
In the comments section of my previous discussion on this topic, many people brought up Tor (The Onion Router). Tor is another tool for privacy, but it operates on a completely different philosophy.
How Tor Works
Imagine you want to send a letter, but you don’t want the recipient to know it came from you, and you don’t want the post office to know who you are sending it to.
Tor works by bouncing your traffic through three random servers (nodes) around the world.
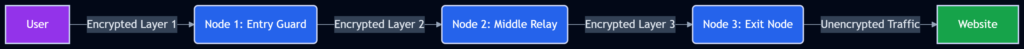
- Node 1 knows who you are but doesn’t know the final destination (it only sees the next hop).
- Node 3 knows the destination but doesn’t know who you are (it sees the request coming from Node 2).
- Node 2 acts as a buffer, ensuring no single node knows both the start and end points.
The Comparison Table
When should you use a VPN, and when should you use Tor? Here is a breakdown:
| Use Case | Best Choice | Why? |
|---|---|---|
| Bypassing Geo-blocks | VPN | VPNs are faster and allow you to pick a specific country (e.g., to watch Netflix US). Tor nodes can be slow and flagged by streaming services. |
| Public Wi-Fi Security | VPN | You want to protect your credit card info at a coffee shop. A VPN encrypts everything securely and quickly. |
| Whistleblowing | Tor | If you are leaking government secrets or exposing corruption, a VPN provider could be compelled by a court to reveal your identity. Tor has no central authority to serve a court order. |
| Everyday Browsing | VPN | Tor is notoriously slow due to the three hops. Browsing normal websites will feel sluggish. |
| High Anonymity | Tor | If you truly need to hide your identity, Tor offers superior anonymity over a commercial VPN. |
Common Use Cases: Real-World Examples
Let’s ground this in reality. Here are specific scenarios and which tool fits best.
Scenario 1: The Coffee Shop Freelancer
You are working at a local cafe using their open Wi-Fi. You need to access your bank account and client emails.
- The Risk: A hacker on the same Wi-Fi network could be “sniffing” packets.
- The Solution: Use a VPN.
- Why: You need to secure the connection between your laptop and the internet. The VPN creates a tunnel that the hacker cannot see into. Speed is also important for work, so Tor would be a hindrance.
Scenario 2: The Traveler
You are traveling to a country with strict internet censorship. You want to read the news from home or access social media sites that are blocked.
- The Risk: The government blocks access to specific IPs.
- The Solution: Use a VPN.
- Why: You can connect to a VPN server in your home country. The ISP in the restricted country only sees encrypted traffic going to a random IP address. They don’t know you are accessing a blocked news site.
Scenario 3: The Privacy Advocate
You are researching a sensitive topic or communicating with a journalist to expose corporate fraud.
- The Risk: You cannot be linked to the communication under any circumstances.
- The Solution: Use Tor (and possibly a secure drop service).
- Why: If you use a VPN, the VPN provider has your identity. If they are subpoenaed, your cover is blown. Tor disperses the trust across three nodes, making it incredibly difficult to trace the connection back to you.
Technical Deep Dive: The Packet Header
I want to circle back to the technical side for a moment because this is where the “myth” of VPN encryption often gets muddled.
When we talk about encryption, we are usually talking about the Payload. But the Header is the traveler’s map. In a standard scenario, the header contains your IP and the destination.
Let’s visualize the header data transformation:
Without VPN:
| Field | Value | Visibility |
|---|---|---|
| Source IP | 203.0.113.45 (Your Home) | Visible to ISP |
| Dest IP | 151.101.1.69 (Website) | Visible to ISP |
| Data | “Hello World” | Encrypted (HTTPS) |
With VPN:
| Field | Value | Visibility |
|---|---|---|
| Source IP | 203.0.113.45 (Your Home) | Visible to ISP |
| Dest IP | 198.51.100.1 (VPN Server) | Visible to ISP |
| Inner Source | 203.0.113.45 | Hidden (Encrypted in Payload) |
| Inner Dest | 151.101.1.69 (Website) | Hidden (Encrypted in Payload) |
| Data | “Hello World” | Double Encrypted |
Notice that the ISP always sees the outer layer. The VPN simply changes the destination on the outer layer to “VPN Server.” This is why the ISP is “blinded” to your final destination.
WrapUP
So, do personal VPNs really protect privacy? The answer is a definitive “it depends.”
It depends on your threat model. If your threat is your ISP selling your metadata, then yes, a reputable VPN is an excellent solution. If your threat is a state-level actor trying to track your every move, a commercial VPN might not be enough, and tools like Tor would be more appropriate.
Using a VPN is a transfer of trust. You are taking your trust away from the ISP and placing it in the hands of a VPN provider. You must choose wisely. Look for providers that have undergone independent third-party audits to verify their “no-log” claims. Be wary of free services, and understand that encryption protects the data, not necessarily your identity if you log into accounts or accept cookies.
Ultimately, a VPN is a tool, not a magic wand. It is a powerful tool, but only when you understand its mechanics and its limitations.
References:
- The Tor Project – Who uses Tor?: https://www.torproject.org/about/history/
FAQs
Does a VPN make me completely invisible on the internet?
No, it does not make you invisible. Think of a VPN more like a tinted car window. People outside (like your ISP) can’t see who is inside the car, but the website you visit (the destination) knows you arrived. If you log into your Google or Facebook account while using a VPN, those companies still know exactly who you are. A VPN hides your connection, not your identity.
If websites already use HTTPS, why do I need a VPN?
This is a great question. HTTPS encrypts the data inside your packet (like your password or credit card number), which is fantastic. However, the “address label” on the outside of the packet—the header—is still visible. Your ISP can see exactly which websites you are visiting, even if they can’t see what you are typing there. A VPN wraps the whole packet, hiding the destination address so your ISP only sees traffic going to the VPN server.
Can my Internet Service Provider (ISP) see what I am doing if I use a VPN?
They can see that you are using a lot of data and that you are connected to a VPN server, but they cannot see where that data is going. They effectively see a scrambled mess. They won’t know if you are browsing a news site, streaming a movie, or banking online. They just see an encrypted tunnel between you and the VPN provider.
Is it safe to use a “free” VPN service?
Generally, no. Running servers and paying for bandwidth costs a lot of money. If a VPN provider isn’t charging you a subscription fee, they have to make money somehow. Often, this means they are collecting your browsing data and selling it to advertisers—the exact problem you were trying to solve by getting a VPN! As the saying goes, “If you aren’t paying for the product, you are the product.”
Does a VPN protect me from computer viruses?
Not really. A VPN secures the “pipe” your data travels through, but it doesn’t check the data itself for malicious software. If you download a virus while your VPN is on, your VPN will happily deliver that virus to your computer. You still need good antivirus software and common sense to stay safe from malware.
Why does my internet connection get slower when I turn on my VPN?
Your data has to travel a longer distance. Normally, you go straight from your house to the website. With a VPN, your data goes from your house to the VPN server (which might be in another country) and then to the website. Your computer also has to spend extra processing power to encrypt and decrypt the data. This extra “hop” and processing naturally cause a slight drop in speed.
What is the difference between a VPN and “Incognito” or “Private” mode?
They do very different things. Incognito mode stops your browser from saving your history, cookies, and form data on your computer. It does nothing to hide you from your ISP or the websites you visit. A VPN hides your traffic from your ISP and masks your IP address from websites. For total privacy, you might need both, but a VPN is what protects your data from the outside world.
How is a VPN different from Tor?
A VPN is like hiring a private driver; you trust that driver (the VPN company) to take you where you need to go without telling anyone. It’s fast and good for streaming. Tor is like taking three different buses with three different drivers who don’t know each other. No single driver knows both where you started and where you ended up. It offers higher anonymity but is much slower, making it bad for streaming or everyday use.
Can I use a VPN to watch shows from other countries?
Yes, this is one of the most popular uses. Streaming services decide what shows to let you watch based on your IP address. If you connect to a VPN server in the UK, the streaming service thinks you are in the UK and will show you the British library of content. However, some streaming services are getting very good at detecting and blocking VPN traffic, so it doesn’t always work.